Updating some backend stuff on the website as well as some article changes to better show what’s new in the tech world. A few minor “look and feel” updates. And removed some coivd-19 verbiage to better reflect new CDC guidelines and the President saying the pandemic is now over.
But as always, if you have special needs due to Covid-19, please let us know so that we may address them and make you feel as comfortable as possible.
Fake Antivirus Bills
Many are getting fake bills that look like they came from popular antivirus and computer companies. These are just attempts to get you to call the phone number in the email and scam you for a subscription you don’t have or already paid for. Ignore these. Do not call the phone number.
Dec 15th 2021 Covid Update
As of this writing all RenoGeek technicians have had their 2 main vaccine shots and the new booster.
As we have done from the start of the pandemic we are more than willing to work with our clients who might need special accommodations, such as contactless service calls, to get us all through these tough times. Feel free to call today to see how we may help you.
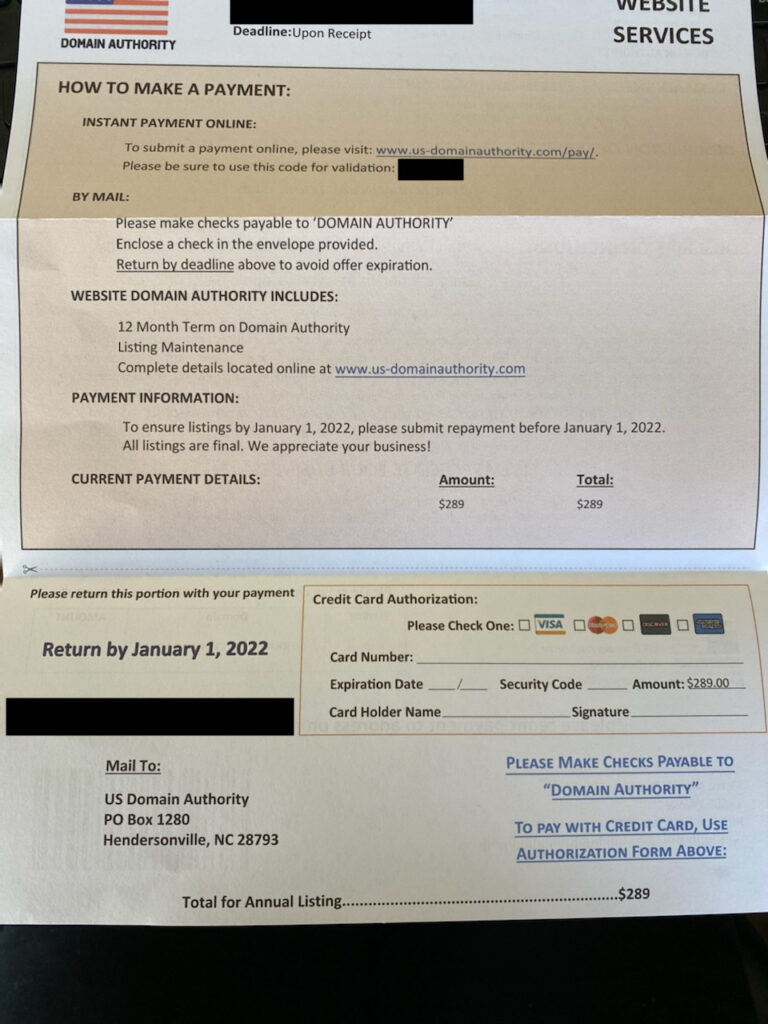
Beware of fake website invoices
I have had a few customers call /email about getting an invoice for their website domain form “us-domainauthority “. com”” for $289.00. It’s 100% fake. Never pay invoices from companies you have never done business with before. Your web developer should be able to tell you when you’ll need to renew again. And for those that don’t get this via snail mail, the scam is also done over the phone with high pressure sales people telling you that you must pay ASAP. Domain renewal never works this way. Stay safe…
8 billion+ passwords leaked…
8.4 billion passwords online leaked — your security may be at risk. A new password leak called “RockYou2021” has exposed 8.4 billion private login passwords.
If your still using the same passwords for all your accounts. It’s time to change them now. Need help? Call RenoGeek to help you setup passwords that won’t compromise all your online accounts.
Regarding Updated CDC covid-19 Mask requirements
As most have heard by now, the CDC has dropped the masking requirements for most kinds of businesses.
While we are sending only fully vaccinated technicians (2x shots + 14 days) to our onsite clients we understand that many are still struggling with the changes that have occurred in all of our daily life over the past 14+ months of the pandemic.
And with that in mind we are more than willing to work with our clients needs and can wear masks onsite if requested. Or as we have already been doing throughout the course of the pandemic, offer free “contactless” pickup and return of your computer equipment.
Feel free to call us at 775-313-1951 with any question you may have or to tell us how we may accommodate your needs.
May 2021 Covid-19 update
All employees are now fully vaccinated. And we are still following all state and local masking and distancing requirements for the safety of our customers. Along with sanitizing our equipment before and after each visit. We are also still offering Contactless pickup and drop-off options.
RenoGeek Computer Repair Covid-19 Protection Measures
RenoGeek is taking the protection of its customers seriously. First by following all current government orders regarding business operation in Nevada. And by constantly sanitizing our repair equipment and using theses CDC recommendations…
Cleaning hands often, with hand sanitizer that contains at least 70% alcohol.
Avoiding contact with people that are sick.
(please only make an appointment if you, your family and employees are feeling well).
Keeping a distance (at least 6 feet) from our clients.
Using new, disposable (one time use) masks, when visiting clients.
Requesting our clients stay safe and also use masks when we are on-site making a service call. As currently mandated by the Government.
Cleaning and disinfecting frequently, clients computer equipment and work surfaces.
Disinfecting clients computers before transport to our shop and again once we return your computer to you (on-site).
Technicians clean with 70%+ alcohol sanitizers before and immediately after client visits. As well as changing into a new mask before seeing each client.
RenoGeek has always had free pickup and dropoff for our clients. Today we are expanding this service to include, “Contactless” appointments.
Where you can just leave your computer at the door and we will pick it up for you. And you can pay with a credit/debit card when it’s returned to you.
(Please call ahead for an appointment for pickup so that we can make sure we can accommodate you and your equipment is not left outside for an extended period of time).
Reno computer Repair by RenoGeek talks about the fake IP renewal scam.

As people start to become more aware of the old Microsoft tech support and virus scams, crooks have had to up their game and find a new way to scam uninformed computer users.
The new scam involves another cold calling technique to trick people into giving up their hard earned money. This new scam starts with somebody from “Tech support” or “Microsoft” calling, who says that you are soon going to loose your “IP address” unless you pay them to renew it.
And like the MS and virus support scams of the past this new scam plays yet again into the lack of knowledge most computer users have about their own systems and how the basics of the Internet work.
Your “IP” address is nothing more than a string of numbers that your ISP assigns to your router or computer to talk with it’s network and the Internet at large. This address is assigned automatically each time your router or computer reboots. And is included in the cost of your Internet bill. So there is no recurring bill you have to pay to keep this IP address. Your ISP gives you a new one each time you reconnect to them. Today, unlike in the past this is all handled automatically and you don’t have to do anything to get or keep your IP address.
So yet again my advice is the same as it has been for years. If somebody calls and says that ANYTHING is wrong with your computer or the Internet, hang up. Don’t talk with them at all. No legit company is ever going to call you about your computer unless you have bought a service contract ahead of time.
Google to try new NeverSlowMode

Google is working on the next update to the chrome web browser and it seems that they are shooting for a much faster user experience.
The new code won’t really speed the rate your data downloads from the internet. But instead, it speeds up the user experience by blocking the biggest data hogs, namely – images, videos, and code such as javascript.
This new mode would (if it works) make the internet a more enjoyable experience by budgeting system resources and render a “quick view” that would limit things from load such as…
Images over 1MB
Stylesheets over 100KB
Scripts over 50KB
The main idea is that page execution beyond these limits would stop processing until a user interacts with the webpage. (Thus a faster load time) Only time will tell if this works in the real world and if such a major change would be long lasting. As most google product seem to suffer from “Code creep” that may add too many exceptions or options to make it useful in the long run.
